I'm going to start putting stuff here that could be of interest to the world at large, and isn't otherwise indexed somewhere (as far as I can tell, anyway).
After going back to my 2011-06-13 post the other day, for the umpteenth time, I happened to notice a curious phrase: this will be fixed in the future.
Alas, I tried both commands on a reasonably modern (5-6 month old) Linux distribution, and lo and behold, both still result in tcpdump: expression rejects all packets.
tl;dr: the syntax to use is still, 13 years later, # tcpdump -i eth0 -nn 'ip6[53:1]=0x02'.
So much for the future.
Inspired by @vkc, I should probably start a links page.
Pardon the dust/brokenness -- I'm migrating my web site to a new host for...reasons. (Yes, I'd rather have it migrated and partially broken than where it was.)
...and I left that job a month ago. 😅
Haven't updated this in a while. I'm back in Minnesota now, albeit with the same job based in Utah.
After some minor shaming from Google, I've tweaked this page's CSS to make it render less awfully on mobile devices. I'm less happy with how it renders on desktop browsers, but it does look substantially better on mobile.
I told my boss (via IM), "IIRC, Asia-Pacific latency [to the US] makes Europe's latency look like kittens puking rainbows."
He responded: ![]()
![]()
Perfect emoji for the moment, courtesy of Skype for Business.
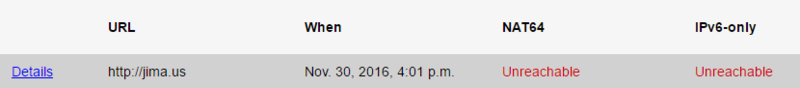
In case anyone noticed this NAT64/IPv6-only failure on nat64check.ipv6-lab.net, it's because my IPv6 tunnel (from SixXS) is having some routing issues. I'd be using the native v6 from my ISP, but thanks to a crappy DHCPv6-PD implementation on the cable modem, I can't get any addresses past my CPE (and routing is broken to/from the cable modem anyway).
IPv6 is still hard for ISPs, it seems.
Update 2016-12-01: Someone re-ran the check and it now shows 100%/100%. No idea who did it -- I was busy at the time.
Today I rediscovered a CGI script I wrote five years ago ![]() . A little hacking/tweaking margins and I got it to do this:
. A little hacking/tweaking margins and I got it to do this: ![]()
After 43 months, I finally got around to updating my IPv6 TLD Hall-of-Shame, for anyone who's into that sort of thing.
Disappointed by the general lack of a cohesive list of IPv6 license plate sightings, I opted to create my own.
It's been a while, so I thought I'd share my Utah IPv6 license plates:
Today I learned that the default IP for a Polycom CMA 4000 after upgrading from version 5.5.0 to 6.0.0 is 192.168.1.254 . It would really have been nice for the documentation to tell me this someplace.
On a CLEARLY unrelated note, I would once again like to thank the author of nmap.
Interestingly, Facebook has taken a two-week head start to World IPv6 Launch: their site is now accessible, by default, from IPv6:
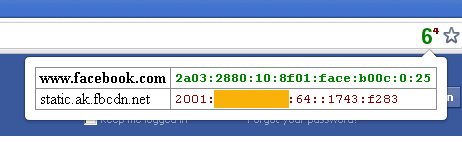
The more astute reader may notice that the IPv6 address for static.ak.fbcdn.net shows up as IPv4. This is a result of me hacking IPvFoo to identify addresses under my NAT64/DNS64 prefix as IPv4 -- which, on the other side of my NAT64 router, they are.
After almost a year, I've updated my IPv6 Top Level Domain (TLD) nameserver hall of shame: https://jima.us/u/v6tlds
Not sure why .vi dropped its IPv6 nameserver(s) ~2011-12-02.
Another site badge, courtesy of The IPv6 Forum:
never mind, broken site
It occurs to me that maybe some of my content doesn't show up various places because I was using v6.jima.us rather than ipv6.jima.us.
I'm shocked and appalled that Google hasn't noticed that my web site is available on an IPv6-only subdomain.
Taking advantage of dot.tk's recent promotion, I went looking for an interesting .tk domain to register. Turns out utah.tk was available. I'm not yet sure what I'm going to do with it, but given my new state of residence it seemed like a worthwhile grab.
I found myself a little disappointed by the lack of search results for Mosquito Penguin LePlatt.
I noticed while trying to detect the start of IPv6 TCP connections on World IPv6 Day last week, that tcpdump doesn't seem to support filtering by both IPv6 and TCP flags. Examples:
# tcpdump -i eth0 -nn 'tcp[13] == 2' and ip6
tcpdump: expression rejects all packets
...wha? Okay, let's try it with an IPv6 netblock instead.
# tcpdump -i eth0 -nn 'tcp[13] == 2' and net 2001:db8::/32
tcpdump: expression rejects all packets
Weird. Alas, further Googling leads to this vague explanation: "Note that tcp, udp and other upper-layer protocol types only apply to IPv4, not IPv6 (this will be fixed in the future)."
This discussion point came up in #ipv6 today, and prox pointed out that there's a way to accomplish this:
# tcpdump -i eth0 -nn 'ip6[53:1]=0x02'
Indeed, out pours all the IPv6 TCP packets with their SYN flags set. Thanks, prox!
He did note that he blogged about the issue in regard to ICMPv6 back in 2009: http://www.prolixium.com/mynews?id=804
Hopefully this post will help others running into the same stumbling block.
After an odd false start with the stock web browser, I have confirmed that the Samsung Galaxy Tab (or the TMO version, at least) does in fact support IPv6 over wifi. Application support may be hit or miss, but I was able to get dual-stack access by installing Mozilla Firefox:
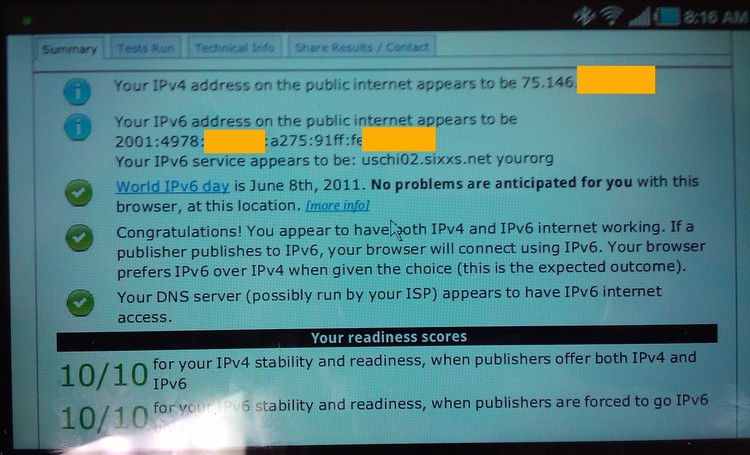
(Sorry it's crooked.)
I'm partial to the T-Mobile variant due to Sprint crippling their firmware -- to the point that you cannot connect HID Bluetooth keyboards (only SPP, Serial Port Protocol). As I already owned a fairly nice HID Bluetooth thumb board, that didn't make me very happy.
I haven't yet tried Firefox on Sprint's Galaxy Tab, but I'll report the results when I do. (I did test the default browser: no IPv6 there.)
EDIT 2011-05-07: I can happily report that the situation is the same on Sprint's Galaxy Tab. Default browser: IPv4-only; Firefox: dual-stack support.
EDIT 2011-08-22: At some point since this post, Sprint issued an update for their Galaxy Tabs enabling HID keyboard support. As far as I know, there is presently feature parity between T-Mobile's and Sprint's devices.
As a result of another discussion in #ipv6, I've learned that the Adobe Flash plugin (at least version 10.2.152.26) is IPv6-compatible.
A little waste of time yesterday (while waiting for a malware scan on another machine):
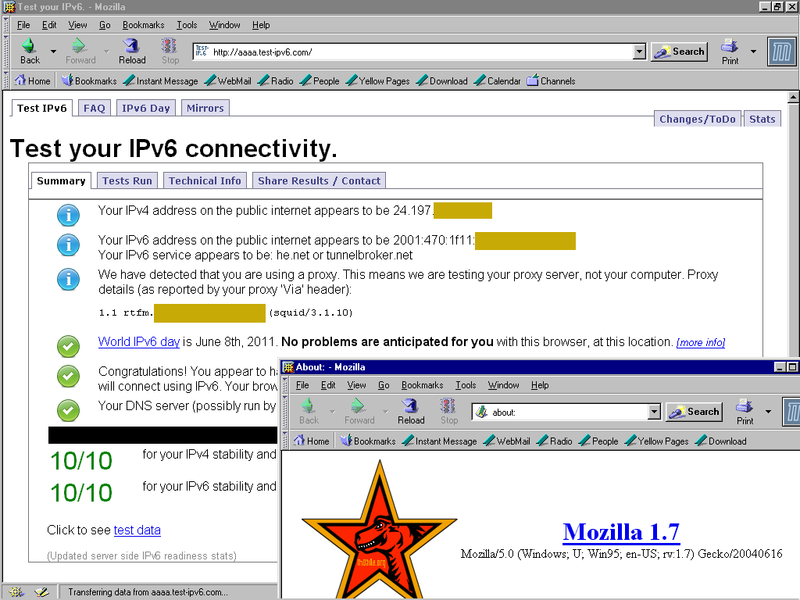
Yep, IPv6 web access on Windows 95.
wasabi in #ipv6 (on freenode) encountered this error when trying to add IPv6 rDNS (reverse DNS) records for a 6to4 block (on 6to4.nro.net):
Either you have entered an invalid nameserver description or the nameserver you refer to has no zone for this reverse delegation.
Everything seemed kosher at face value, but eventually we figured out that the problem was that the hostnames he was entering didn't match the NS records in the zone -- in this case, autogenerated by MS DNS and unchangable. The solution that worked was to use the hostnames from the NS records.
EDIT 2011-02-24: While testing this for myself, I found that the issue wasn't that the names didn't match, but that there was a third NS record in the zone, but not submitted in the form. Non-matching names: fine. Extra NS record: error.
EDIT 2011-02-24 #2: It seems there may be some other factors at play here that can cause that error. I can't claim to know all of them, and as of yet I seem to be the authoritative source for help on that error message. I'll be happy to help anyone who runs into it. ;-)
EDIT 2011-10-11: Random internet user freerodent (who found this page via Google, since it's still the only hit for the error) reported to me that he encountered this error -- albeit inconsistently -- when trying to use afraid.org's nameservers. The best running theory from the #ipv6 peanut gallery is that their nameservers are overloaded, and/or may have been briefly down/laggy when 6to4.nro.net did its check.
Lesson learned today: CentOS can in fact go IPv6-only, but you have to overcome several issues:
- mirrorlist.centos.org is IPv4-only
- All of the "addons" mirrors are IPv4-only
- All of the "extras" mirrors are IPv4-only
- Yum + SSL is IPv4-only (doesn't even do an AAAA lookup)
1-3 can be resolved by faking out DNS and using mod_proxy on a dual-stacked server. For the last one I had to un-SSL the mirrorlist URL for my personal repositories (and the mirrors it reports).
Happily, I can report that there is at least one IPv6-connected mirror for "base" and "updates," and Fedora's EPEL (Extras Packages for Enterprise Linux) has IPv6 on its mirrorlist server and at least one mirror.
Happy birthday to my good friend of almost 16 years, Rich D. Hopefully someday we'll actually meet in person!
Windows 7 seems to be picky about what it considers "Internet access;" IPv6 apparently falls short, by its standards: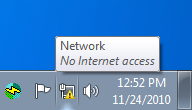
It continues to sadden me to see how far North America (that is, ARIN region) is lagging behind on IPv6 adoption. Case in point: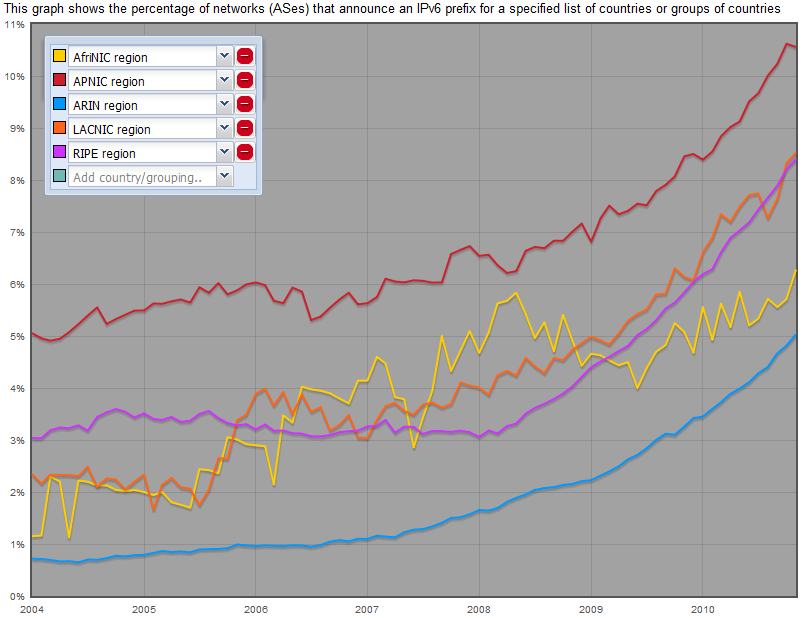
-!- EnricoNirvana has joined #aurora
<EnricoNirvana> +ns
<EnricoNirvana> ?
<EnricoNirvana> none ?
<EnricoNirvana> is this channel used ?
<jima> we prefer the term "pre-owned."
<EnricoNirvana> oh
<EnricoNirvana> sorry
Log snippet from Monday:
<nate> anyone done any work with dll injection?
<jima> only at the federal government's behest.
The conversation didn't go any further. Pity.
Hint to authors of Chrome extensions: it's not a functional equivalent to ShowIP for Firefox if it doesn't support IPv6. Just sayin'.
Couple posts today (so far).
My car rolled to 121,000 miles today just outside the gas station. It's funny; up until this one (purchased new in 2004), that's about when I've usually acquired cars.
As Natck mused on TMBO: "the completest in me would like to have a B: drive listed in Windows Explorer."
The 13th passed without significant note. I'll consider myself lucky.
Happy Friday the 13th, everyone!
I just discovered, while doing some unfortunate testing, that Internet Explorer 5.0, from a stock installation of Windows 2000 Professional SP4*, supports IPv6. Consider my mind boggled.
* plus the IPv6 stack designed for SP1
Despite all the crap I give him for his seemingly endless reposts, I will give Coyote props when he posts fresh, funny content. Thanks, Coyote!
Matthew Miller once again caused me to wander off on a tangent.
While I find myself liking Jem's 'They' (discovered via cheesy reality TV), for some reason I have trouble taking her very seriously.
Seems like she's old enough to have known better, although maybe she assumed her target audience isn't.
You might not have enough bits in your IP address if you can't reach my SSL site. Just saying.
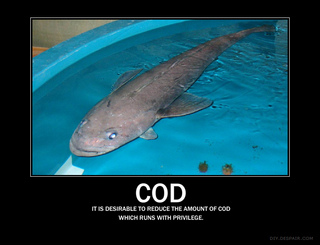
Apparently I helped a meme get off the ground today:
(Caption: "It is desirable to reduce the amount of cod which runs with privilege." [sic])
Originated here, linked here. Source image here, assembled here.
In unimportant, uninteresting news, I've decided to move my web stuff from beer.tclug.org/jima/ to jima.us/ .
Three links today!
- Throwing a reference up to Amanda's Links page.
- TCLUG ostensibly has a Twitter feed, which can be found here (or if you'd like to be offended, here).
- dragorn (of Kismet fame) is working on a fun project over on Google Code involving Smart Card research.
Despite the unfortunate date, today I'm going to link to my good friend Bill Lemieux's blog, Megajoules & Gigawatts. Bill's something of a Mad Scientist, tinkering with high voltage energy, magnetic fields, and lasers. Yes, freakin' lasers.
IMO, all that makes him more of a Mad Engineer, but regardless, he's a smart guy -- and to be honest, a lot of the technical bits go way over my head.
My Seattle-based photography buddy Joseph Graziano's web site can be found at http://faustomatic.com/, and his blog at http://photosbyfaust.wordpress.com/
If you're here looking for the TMBO abbreviations listing, it can be found here.
To go full circle, apparently jer_ has also put MTCFF up for the world to see.
For those who know him, my friend Ryan (Chi)'s site is infectious.cc.
There seems to be some confusion in the TMBO community about what "MTCFF" means. To summarize: Male TMBO Creepy Fuck Factor. See here no, here for more TMBO-related abbreviations.
I finally found a single reference to Hacker #139 online. Oddly, this didn't show up on Google at all. (I found it via Yahoo.)
I was having a discussion with another sysadmin today, when he mentioned in passing something about Secure Computing Corporation. I made some off-hand reference to my "hacker #139" beanie, which evidently confused him. A quick Google made me realize that probably only a handful of people have ever heard of these things.
Back in 1997 or thereabouts, Secure Computing had some sort of open house event at their corporate headquarters (when they were still in Roseville, MN). I was merely a geek in high school, but my mother liked to promote my interest in computers, so she took me there. Among food, drinks, and promotional literature, they were giving out souvenir beanie hackers, with the company's logo and web site address on one side, and "HACKER #139" on the other. It was made up to look like a chalk outline of a late technological ne'er-do-well, presumably after mincing packets with SCC.
As probably everyone else did, I took one. And now, 10 or so years later, I suppose I can consider myself fairly fortunate to still have it:
It's been sitting on my computer at work for maybe 6 or 7 years. I've never really thought anything of it; it didn't occur to me that it was an obscure, unknown object.
And now for some backfill:
Here's a link to pictures of my wang. Because I know everyone wants to see them.
Ask us how you can PIMP YOUR SPARC!
Taking the Information Superhighway to, err, the rest stop
PRESS RELEASE
We at Minty Green Media are proud to announce the latest in Broadband Technology. Most consumers have at least heard of FTP (File Transfer Protocol). Some of the more well-versed of you are familiar with FTTP (Fiber To The Premises). Today we bring to you an all-new concept: FTTTP!
Fiber To The Toilet Paper
To save others and myself some time, I'll pre-emptively answer some questions.
- Yes, this is a joke.
- Yes, that link light is on. The fiber is lit.
- I was bored, and wondered how far my longest fiber optic cable went. It can actually reach from my computer room on the ground floor to my pile-o-boxen in the basement...the long way (those who've been to my house can somewhat understand how far that is). So if I needed to (cat5 b0rk4g3 in the wall), or, for whatever sick reason, wanted to connect the machines downstairs with fiber, I could. (I'd just have to deal with phemale killing me. Minor detail.)
- The joke only occurred to me after I put the transceiver down on the nearest open surface (i.e., a roll of TP).
Now I'll sit back and wait for the venture capitalists to start calling. *crickets chirping*
My parody of spam hawking Norton as the SoBig [virus] Killer. Yeah, whatever.
There seems to be some continued interest (at least from spiders) in my SparcStack.
Here's a link to older pictures of my wang. You know I share the love.